See what’s exposed.
Fix what matters.
Stay ahead of risk.
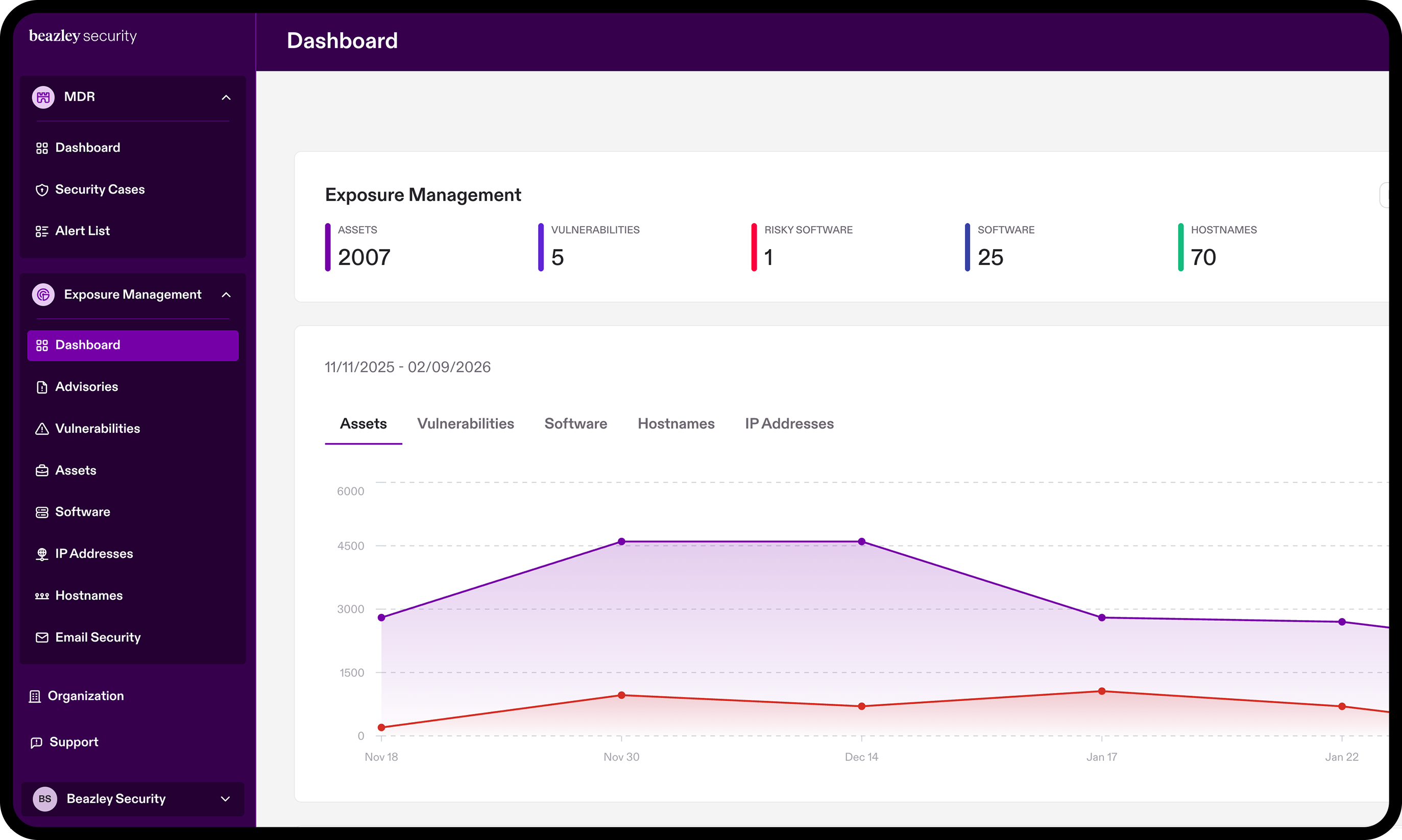
Continuously identify, track, and reduce critical risks across your external attack surface
As time goes on, new assets, shadow IT, and legacy infrastructure can silently introduce risk into organizations with even the most familiar environments. From unpatched servers to forgotten subdomains, unknown factors in your attack surface can provide attackers a foothold. Fueled by AI, threat actors are finding new vulnerabilities to exploit faster than ever. Protecting your organization requires accelerating your response to the exposures that are most likely to cause incidents.
Beazley Security’s Exposure Management platform provides continuous, automated visibility into your organization’s internet-facing footprint: domains, IPs, exposed services, and externally accessible software. It goes beyond simple asset discovery, integrating intelligence from Beazley Security Labs to highlight the exposures that matter most and guide focused, effective risk reduction.
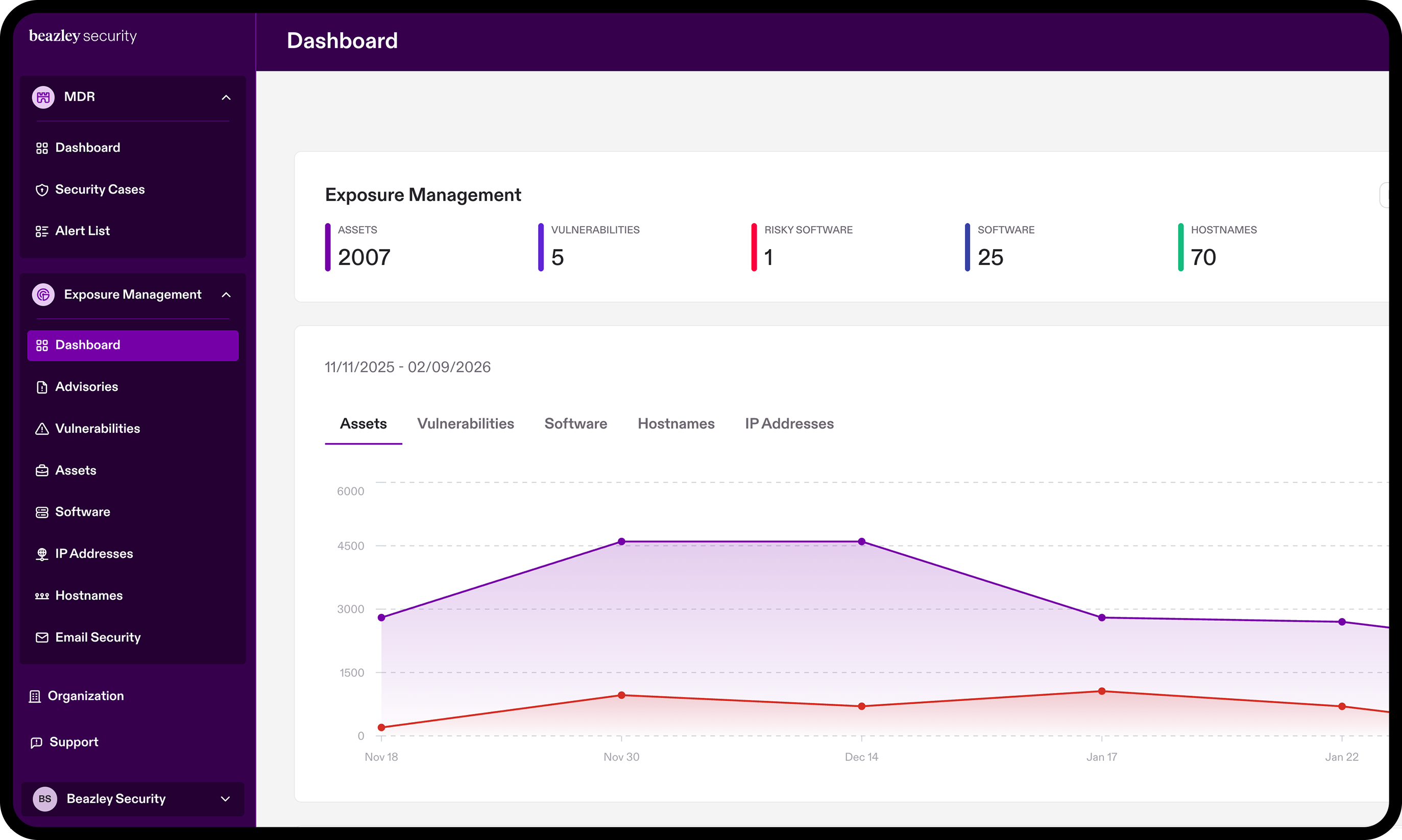
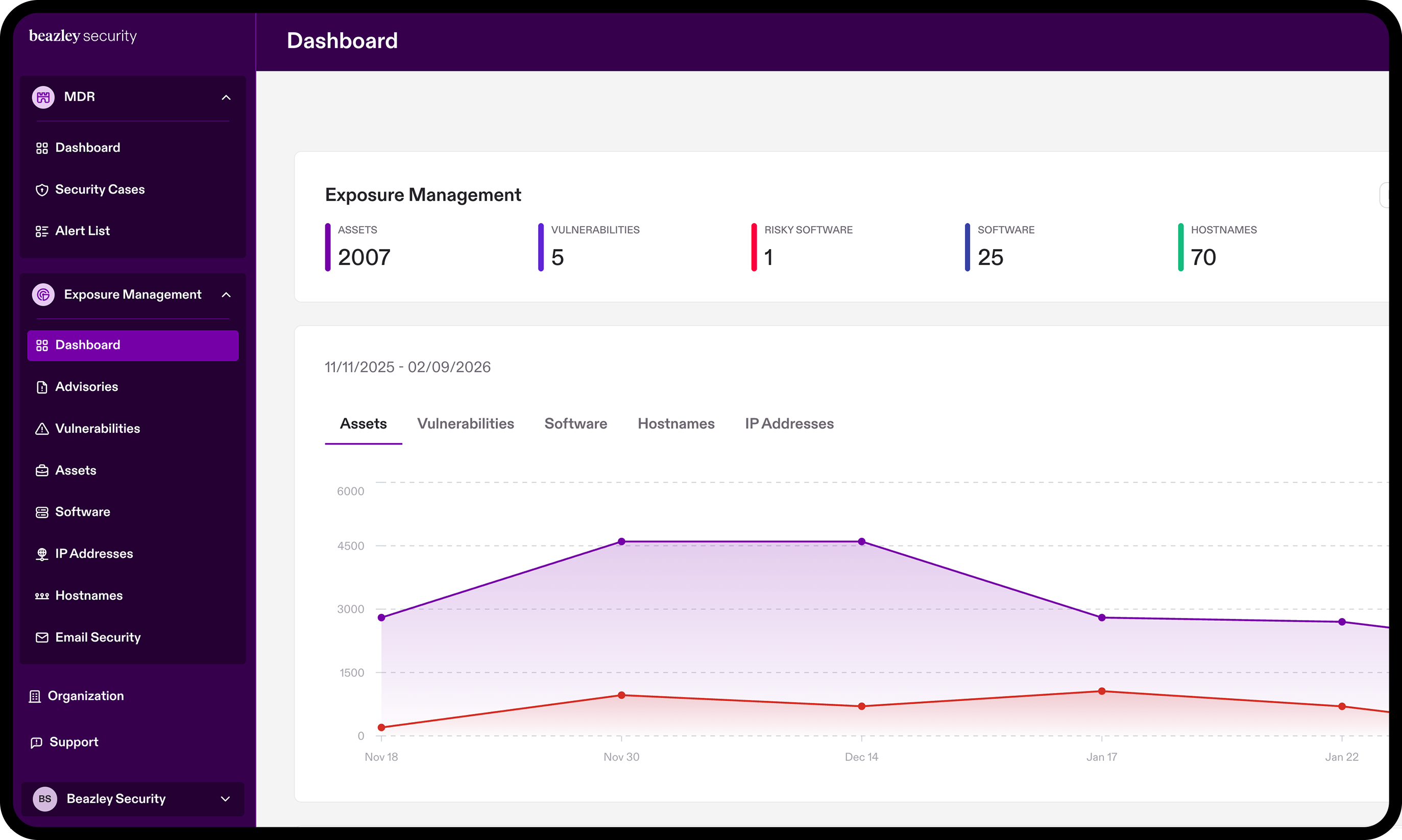
Exposure Management at a glance
Automated discovery of externally exposed assets, including those not previously known or tracked
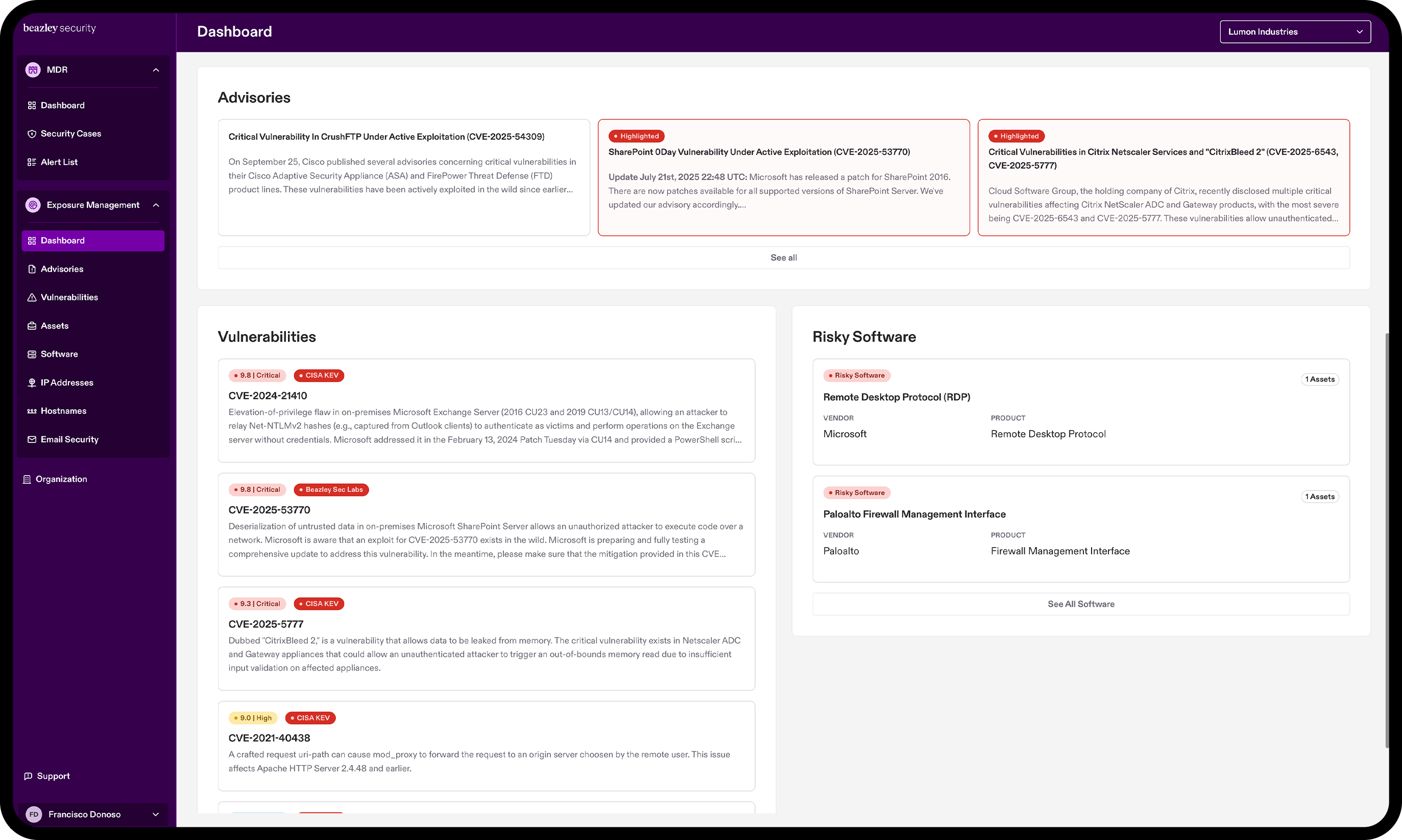
Threat-contextualized prioritization using intelligence from Beazley Security Labs, focusing attention on exposures aligned with active attacker campaigns
Early identification of emerging exposure patterns before they are widely abused
Reduced alert fatigue by filtering out low-impact findings unlikely to be exploited
Personalized notifications based on critical risks and emerging threats affecting your Internet-facing infrastructure
Get complete visibility and control your external attack surface
Automate discovery of your attack surface
Exposure Management continuously scans your externally-facing assets to provide a comprehensive view of your attack surface in near real time. With no agent deployment, internal network access, or manual IP address input required, it uncovers:
- All subdomains and CNAMEs associated with your organization’s monitored domains
- Any unpatched Known Exploited Vulnerabilities across externally-facing assets
- Misconfigured security certificates and unmanaged infrastructure
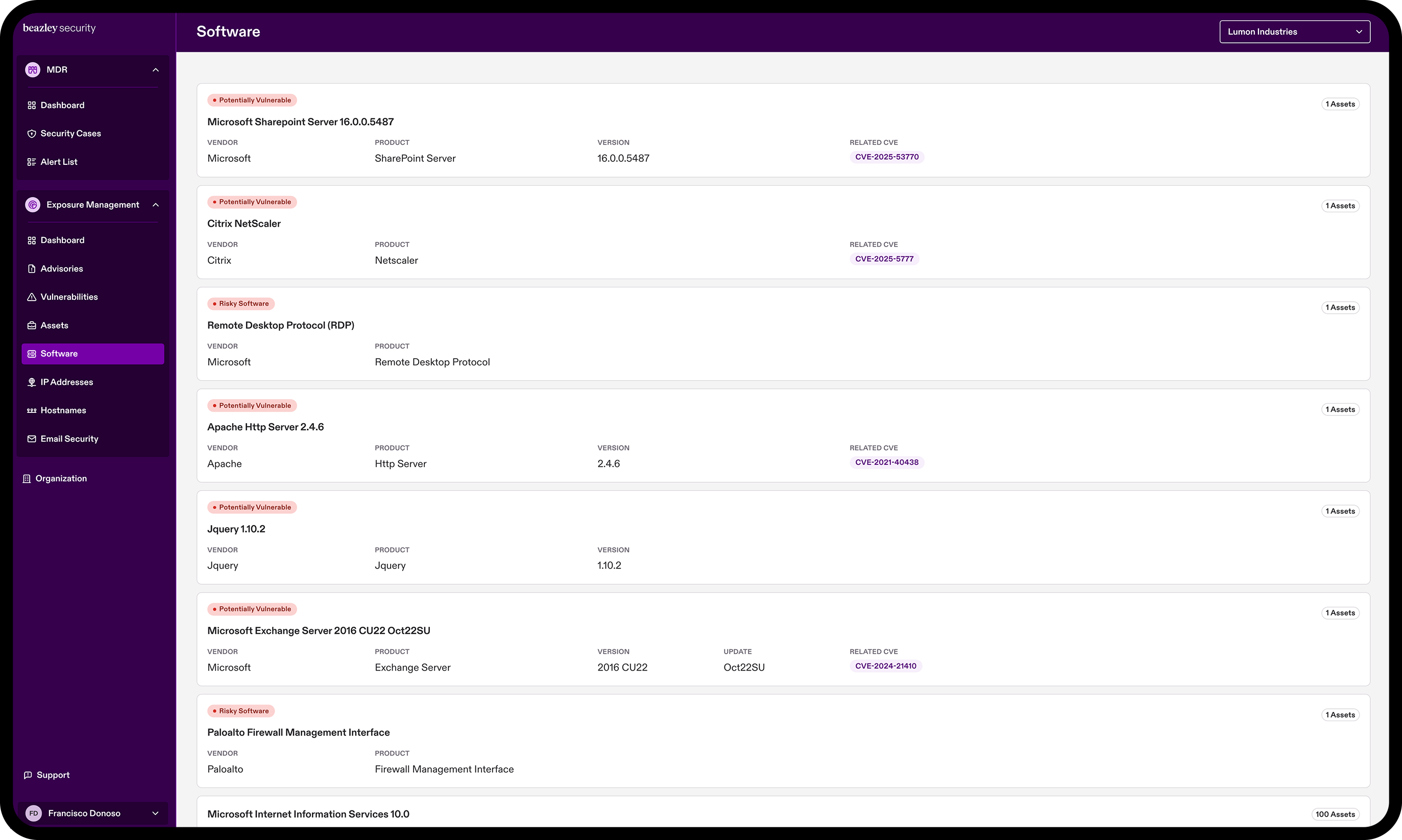
- A software inventory with detailed insights into all discovered IPs, hostnames, and version data
Every scan contributes to your security posture evaluation, providing clear visibility into outstanding security issues. By having near real time visibility to changes to your attack surface, along with proactive prompts and curated intelligence on known exploited vulnerabilities that affect your environment’s assets, your IT and security teams can take action to mitigate threats. This pre-emptive approach is essential to addressing potential risk before it can materialize.
Maximize security value by pairing Exposure Management with MXDR

Tailored to real-world risks in your environment
It’s not always clear how much risk a security issue poses. That’s why Exposure Management combines automation with expert insights and risk scoring from the team inside Beazley Security Labs. Based on our experience handling thousands of security incidents, Exposure Management can ensure organizations understand their exposure, as well as how to best prioritize and address them.
This includes:
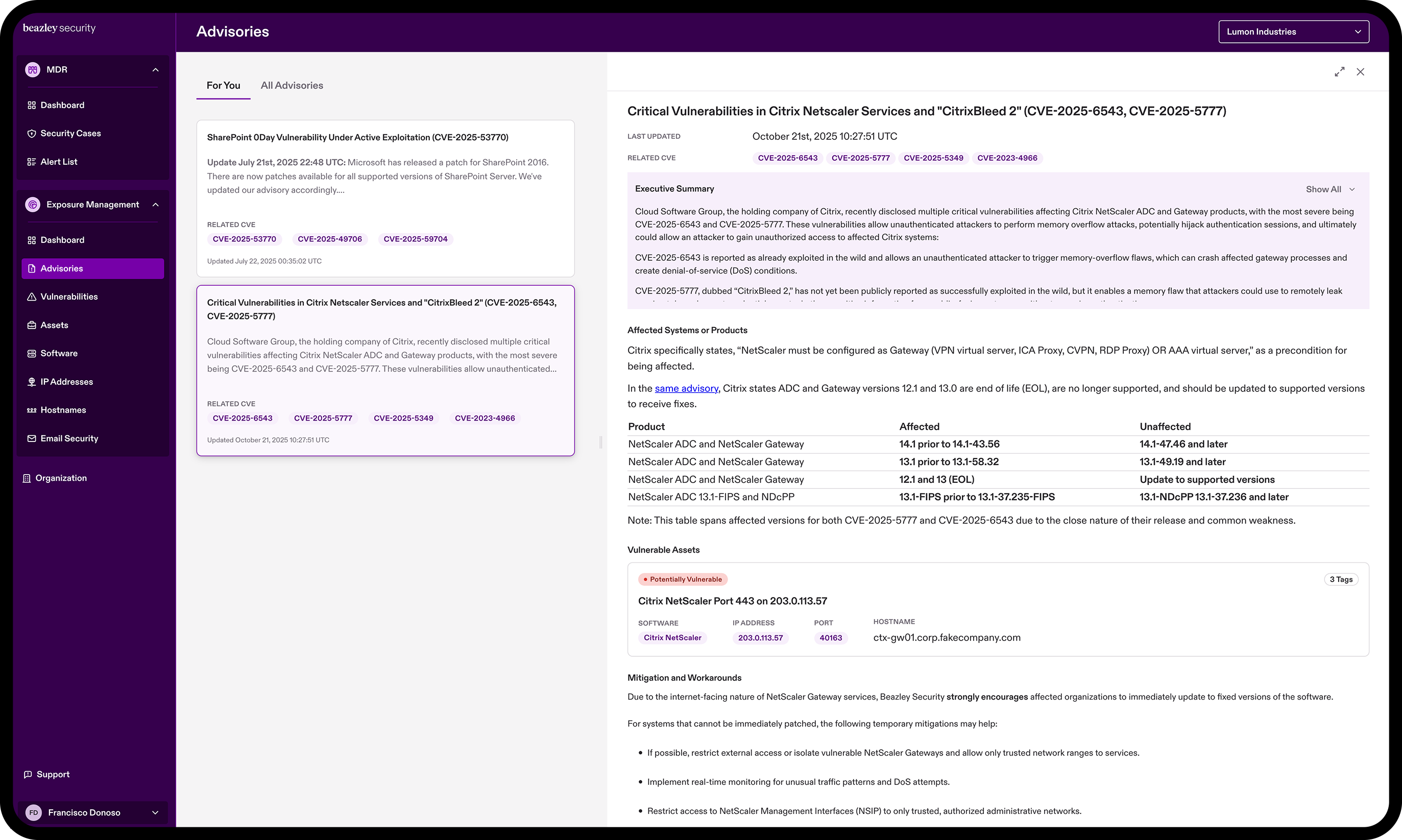
- Automated exploited vulnerability and advisory alerting specific to your environment
- Visibility to exposures and intelligence on mitigation activities
- Autocorrelation of known vulnerabilities with discovered assets

Don’t get stung by shadow IT
Old servers, forgotten subdomains, and unmanaged assets are often silent sources of security risk. Exposure Management uncovers and flags these risks instantly, prompting asset owners to patch, reconfigure, or decommission infrastructure before it becomes a target for bad actors.
- Rediscover long forgotten servers
- Reclaim control of shadow IT
- Bridge the external edge monitoring gap
Exposure Management shines a light on every corner of your external attack surface, helping you reduce security risk, harden against cyber attacks, and effectively prioritize your security resources.
How Beazley Security Exposure Management works
Schedule a demo and take back control of your external attack surface
Cyber visibility for every stage of growth
Whether you're establishing your core security practices or optimizing a mature program, Exposure Management delivers the external attack‑surface visibility that aligns with your needs.
Coming Soon: Extend Risk Monitoring to third-party suppliers

Risks associated with third parties and trusted vendors is a leading cause of security incidents and breaches. As an extension of Exposure Management, Beazley Security is launching a companion Third Party Risk Monitoring product to evaluate key suppliers for security issues that could impact your organization.
- Add and continuously monitor key suppliers directly in VERACIS
- Monitor vendor security posture in near real time with dynamic scoring based on their access to your corporate systems, the sensitivity of data that they can access, and criticality to your operations
- Provide a detailed vendor security posture report so you can work with your vendor to quickly remediate issues that may affect your organization’s exposure
By objectively assessing vendors, including factors such as their risk profile, level of integration to your environment, and importance to your business objectives, you’ll be armed with the insights and information necessary to minimize threats targeting third parties.

